
The specialists of the information security company Check Point presented a detailed description of the DoubleFeature system, designed to register various stages of post-exploitation associated with the deployment of DanderSpritz. DanderSpritz is a full-featured post-exploitation framework, malware environment from the Equation Group's APT arsenal, which is affiliated with the US National Security Agency (NSA).
For the first time, DanderSpritz became known on April 14, 2017, when the hacker group Shadow Brokers published the tools stolen from the NSA. The leak also contained the NSA-developed exploit EternalBlue, which made possible a massive attack by NotPetya ransomware in June 2017.
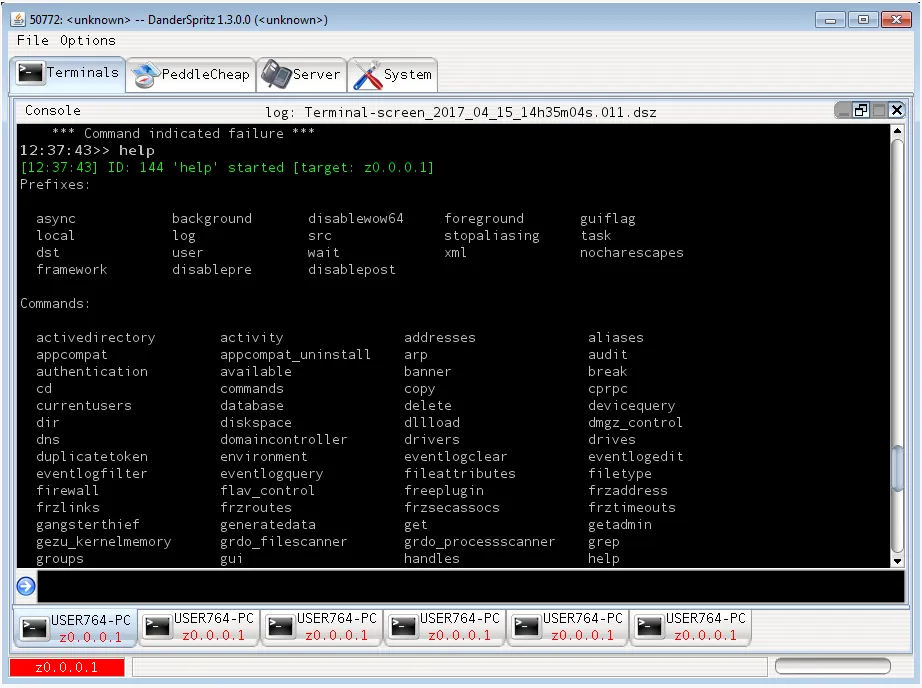
DanderSpritz is a modular, discreet, fully functional framework based on dozens of plugins for post-exploitation activities on Windows and Linux hosts. One of them is DoubleFeature, a diagnostic tool for machines infected with DanderSpritz.
As the researchers explained, DoubleFeature acts as a kind of "Rosetta Stone" to better understand the DanderSpritz modules and the systems they compromise.
“This is just a blue dream for incident response teams,” the researchers said.
The DoubleFeature tool, designed for logging tools that are deployed on an attacked machine, is a control panel in the Python programming language. Among other things, the panel also acts as a reporting utility for extracting information from logs and uploading them to a server controlled by attackers. The output is interpreted using a custom executable file DoubleFeatureReader.exe.
Plugins monitored by DoubleFeature include -
UnitedRake (second name EquationDrug): UnitedRake (UR) is a remote access tool that can be used to target Windows machines. It is an extensible and modular framework that is provided with a large number of plugins that perform different information collection functions.
PeddleCheap: PeddleCheap is among the first tools to be run on a victim machine, and can be used to bootstrap a complete DanderSpritz installation. PeddleCheap has minimal functionality allowing attackers to connect to the victim machine and remotely install and configure implants that allow further post-exploitation functionality, including a full install of the DanderSpritz framework.
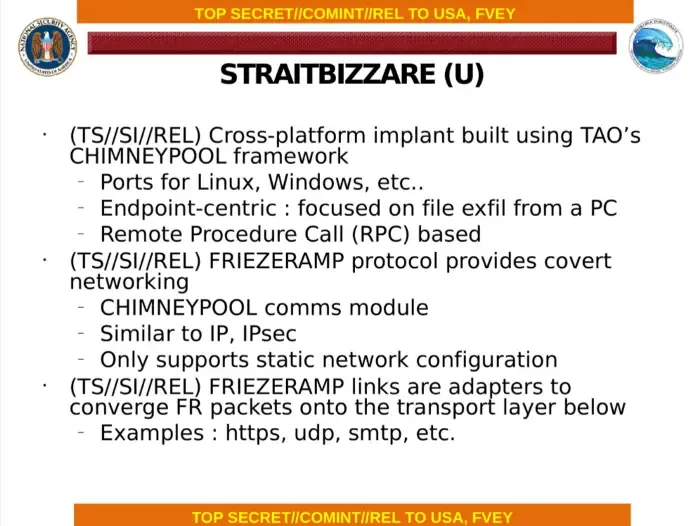
StraitBizarre: StraitBizarre (SBZ) is an implant used for stealthy data exfiltration which is performed over FriezeRamp – a custom network protocol that is similar to IPSEC. It’s a cross-platform project, and different versions exist supporting Windows, Linux, and mobile platforms.
KillSuit (aka GrayFish): KillSuit is an unusual plugin in that once deployed on the victim machine, its entire mission is running other plugins, providing a framework for persistence and evasion. Some DanderSpritz plugins can be either run individually or be invoked through KillSuit.
DiveBar: DiveBar (DiBa) is a persistence toolkit, DoubleFeature’s name for the part of KillSuit responsible for persistence methods
FlewAvenue: FlewAvenue is an IPv4 driver that provides covert network access for other tools. It provides different networking faculties such as DNS queries and ICMP echo (ping).
MistyVeal is an implant validator, which checks the compromised system for authenticity.
Apart from the above extension more three plugins are there namely - DuneMessiah, CritterFrenzy, and DiceDealer.
“Sometimes the world of high-end APT tools and the world of common malware appear to be two parallel universes. Government-funded factions typically operate huge secret codebases with a huge set of functions that have been in use for more than a decade out of practical necessity. It turns out that we are still slowly digesting the leak from four years ago, which revealed to us DanderSpritz and get new ideas, "- noted the researchers.