
Upon being notified of the misconfiguration, Microsoft quickly secured the endpoint. The software company mentioned that data exposed due to misconfigured endpoint includes names, email addresses, email content, company name, and phone numbers, and may have included attached files relating to business between a customer and Microsoft or an authorized Microsoft partner.
On the blog post, Microsoft noted that -
"Our investigation found no indication customer accounts or systems were compromised. We have directly notified the affected customers."
"The issue was caused by an unintentional misconfiguration on an endpoint that is not in use across the Microsoft ecosystem and was not the result of a security vulnerability. We are working to improve our processes to further prevent this type of misconfiguration and performing additional due diligence to investigate and ensure the security of all Microsoft endpoints."
BlueBleed: Largest PII Data Leaks
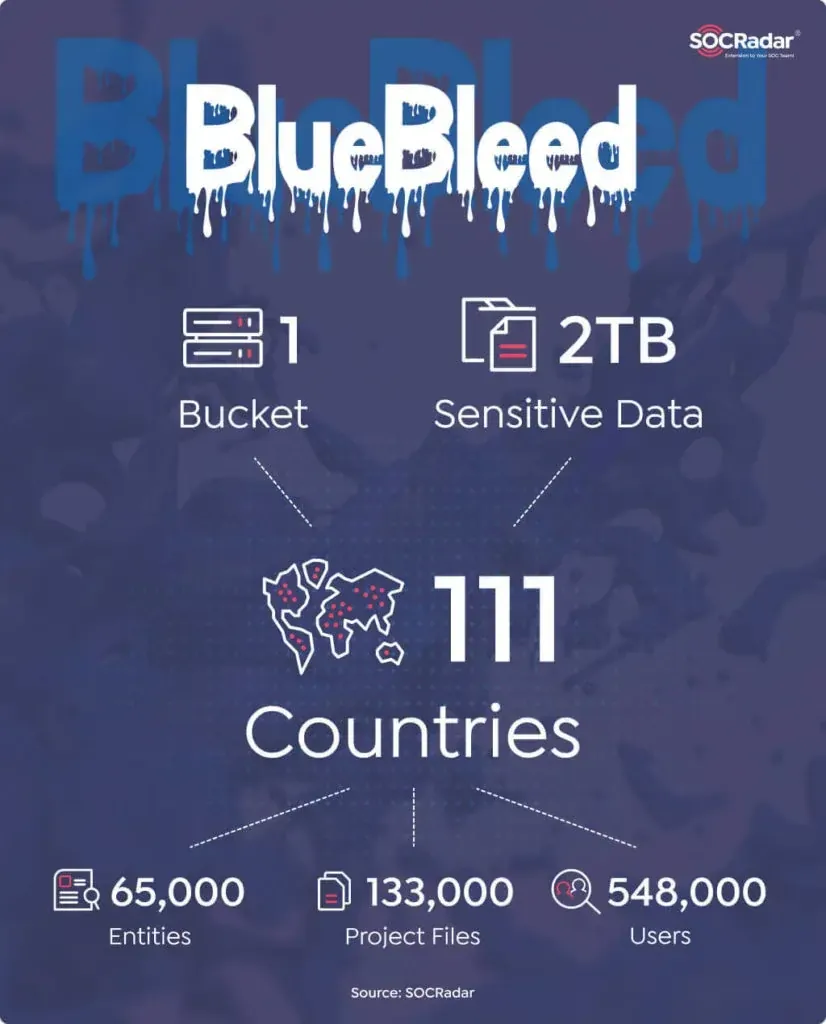
As this misconfigured endpoint was discovered by the SOCRadar, they have also published a post stating that they detected sensitive data of 65,000 entities due to a misconfigured server.
The leak includes Proof-of-Execution (PoE) and Statement of Work (SoW) documents, user information, product orders/offers, project details, PII (Personally Identifiable Information) data, and documents that may reveal intellectual property.
SOCRadar's Cloud Security Module detected multiple public buckets exposing the customer data, and amongst that six large ones contained information for more than 150,000 companies in 123 different countries. According to the experts of cyber security services in Singapore, protecting customer information is the most important element of a collaboration tool.
SOCRadar named the leak as BlueBleed, a term referring to the sensitive information leaked by six misconfigured buckets collectively.
SOCRadar noted that The first part of the collection is due to a misconfigured Azure Blob Storage. It can be considered one of the most significant B2B leaks, affecting more than 65,000 entities in 111 countries with sensitive data inside a single Bucket.
BlueBleed leaks include critical data such as project details, signed customer documents, and customer emails. The exposed data, if parsed properly, enable threat actors to create elaborate attacks against the companies at risk of BlueBleed. Even though most of the data consists of RAW files of databases, the threat actors certainly have enough resources to parse and process the data
Exposed Data Available via Search Tool
On September 24, 2022, SOCRadar’s built-in Cloud Security Module detected a misconfigured Azure Blob Storage maintained by Microsoft containing sensitive data from a high-profile cloud provider.
In this, SOCRadar researchers found a bucket where SQLServer backups are stored, and upon further initializing the backups, they found links between the misconfigured bucket and other Azure Blob Storages. This misconfigured bucket and other Azure Blob Storages exposed the sensitive data of tens of thousands of companies.
SOCRadar has released a search tool named BlueBleed, where companies can search their company names to see if they are impacted by any of the BlueBleed leaks.
What is BlueBleed?
The term BlueBleed has been given by the SOCRadar team to the sensitive information leaked by six misconfigured buckets collectively. SOCRadar's in-house cloud security module detected multiple misconfigured servers containing sensitive data, including Azure Blob Storage, Amazon AWS S3 Buckets, and Google Buckets. The six largest buckets of those leaks are collectively called BlueBleed.
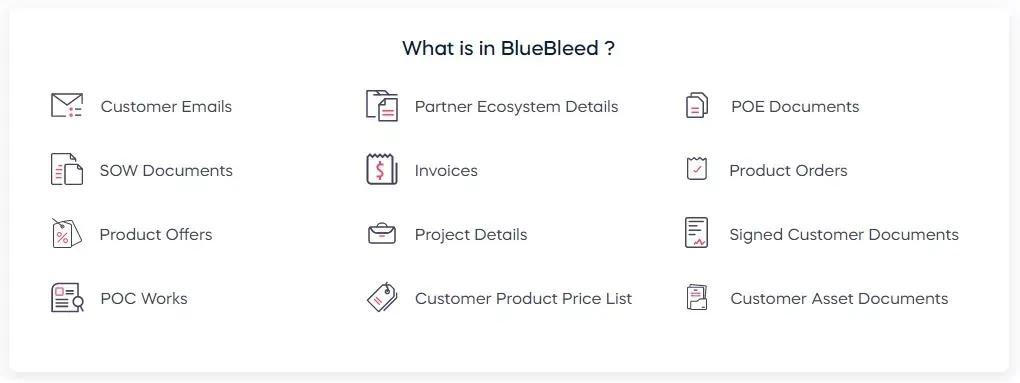
Data includes in BlueBleed leaks
According to the SOCRadar, the misconfigured server, SQLServer databases, and other files belonging to Microsoft exposed 2.4 TB of sensitive information. The exposed data include files dated from 2017 to August 2022.
SOCRadar noted that the leak, dubbed BlueBleed Part I, consists of critical data belonging to more than 65,000 companies from 111 countries, that includes more than 335,000 emails, 133,000 projects, and 548,000 exposed users within the leaks so far.
The exposed files in the misconfigured bucket include;
- POE documents,
- SOW documents,
- Invoices,
- Product orders,
- Product offers,
- Project details,
- Signed customer documents,
- POC (Proof of Concept) works,
- Customer emails (as well as .EML files),
- Customer product price list and customer stocks,
- Internal comments for customers (High risk etc.),
- Sales strategies,
- Customer asset documents, and
- Partner ecosystem details.
Microsoft's Disappointment with SOCRadar
Microsoft started notifying affected customers and also provided them with instructions for contacting Microsoft with questions or concerns. But at the same time, Microsoft is criticizing SOCRadar for allegedly “exaggerating” the scale of the leak.
Microsoft is disappointed that SOCRadar has chosen to release publicly a “search tool” stating that is not in the best interest of ensuring customer privacy or security and potentially exposing them to unnecessary risk.