Google says -
"Project Zero’s mission is “make 0day hard”. 0-day will be harder when, overall, attackers are not able to use public methods and techniques for developing their 0-day exploits."
Broken the Record for in-the-wild Zero-days
According to Project Zero, 2021 was a Record Year for in-the-wild Zero-days. 2021 included the detection and disclosure of 58 in-the-wild 0-days, the most ever recorded since Project Zero began tracking in mid-2014. This is more than double the previous maximum of 25 detected in 2020.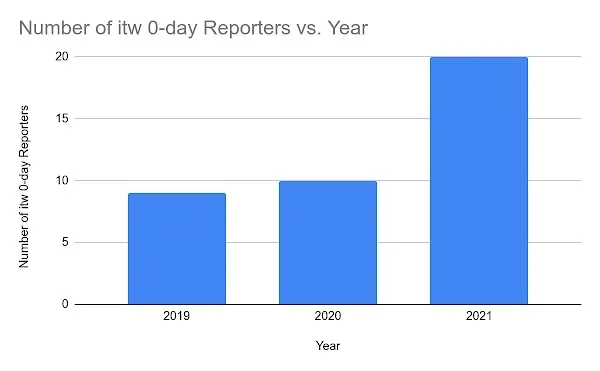
With this record number of in-the-wild 0-days to analyze Project Zero team saw that attacker methodology hasn’t actually had to change much from previous years. Attackers are having success using the same bug patterns and exploitation techniques and going after the same attack surfaces.
On analyzing these 58 0-days used in 2021, the team found that these 0-days are similar to previous & publicly known vulnerabilities. Only two 0-days stood out as novel: one for the technical sophistication of its exploit and the other for its use of logic bugs to escape the sandbox.
There are more factors than just the use that contribute to an increase in that number, most notably: detection and disclosure. Better detection of 0-day exploits and more transparently disclosed exploited 0-day vulnerabilities is a positive indicator for security and progress in the industry.
Labeling or Annotating Vulnerabilities in Security Advisories
The number of detected in-the-wild 0-days has increased due to more disclosure of these vulnerabilities. Labeling vulnerabilities in the security advisories by vendors, with the information about potential in-the-wild exploitation, helps to track and get clear information regarding in-the-wild 0-days. Apple, Google Android, Microsoft, Google Chrome, Apache, and Adobe who have been annotating their security bulletins for transparency.
In-the-wild 0-days in Qualcomm and ARM products were annotated as in-the-wild in Android security bulletins, but not in the vendor’s own security advisories.
Project Zero team noted, "it's highly likely that in 2021, there were other 0-days that were exploited in the wild and detected, but vendors did not mention this in their release notes." But in 2022, the team hopes that more vendors start noting when they patch vulnerabilities that have been exploited in-the-wild.
Popular and well-known Vulnerabilities
Out of the 58 in-the-wild 0-days for the year, 39, or 67% were memory corruption vulnerabilities. Memory corruption vulnerabilities have been the standard for attacking software for the last few decades and it’s still how attackers are having success. Out of these memory corruption vulnerabilities, the majority also stuck with very popular and well-known bug classes:
- 17 use-after-free
- 6 out-of-bounds read & write
- 4 buffer overflow
- 4 integer overflow
The following are the major platform that the team saw in-the-wild 0-days for this year.
Chromium (Chrome): Chromium had a record high number of 0-days detected and disclosed in 2021 with 14. Out of these 14, 10 were renderer remote code execution bugs, 2 were sandbox escapes, 1 was an info leak, and 1 was used to open a webpage in Android apps other than Google Chrome.
The 14 0-day vulnerabilities were in the following components:
- 6 JavaScript Engine - v8 (CVE-2021-21148, CVE-2021-30551, CVE-2021-30563, CVE-2021-30632, CVE-2021-37975, CVE-2021-38003)
- 2 DOM Engine - Blink (CVE-2021-21193 & CVE-2021-21206)
- 1 WebGL (CVE-2021-30554)
- 1 IndexedDB (CVE-2021-30633)
- 1 webaudio (CVE-2021-21166)
- 1 Portals (CVE-2021-37973)
- 1 Android Intents (CVE-2021-38000)
- 1 Core (CVE-2021-37976)
WebKit (Safari) : In 2021 there were 7 publicly known in-the-wild 0-day targeting WebKit/Safari. In 2021’s WebKit bugs in the context of other Safari bugs not known to be in-the-wild and other browser in-the-wild 0-days.
The 7 in-the-wild 0-days targeted the following components:
- 4 Javascript Engine - JavaScript Core (CVE-2021-1870, CVE-2021-1871, CVE-2021-30663, CVE-2021-30665)
- 1 IndexedDB (CVE-2021-30858)
- 1 Storage (CVE-2021-30661)
- 1 Plugins (CVE-2021-1879)
Internet Explorer: Internet Explorer has had a pretty consistent number of 0-days each year. 3 of the 4 0-days seen in 2021 targeted the MSHTML browser engine and were delivered via methods other than the web. Instead, they were delivered to targets via Office documents or other file formats.
The four 0-days targeted the following components:
- MSHTML browser engine (CVE-2021-26411, CVE-2021-33742, CVE-2021-40444)
- Javascript Engine - JScript9 (CVE-2021-34448)
Microsoft Windows: Windows is one of the most targeted platforms for cyber crooks, as this has the highest number of users that puts it in the target.
In 2021 there were 10 Windows in-the-wild 0-days targeting 7 different components:
- 2 Enhanced crypto provider (CVE-2021-31199, CVE-2021-31201)
- 2 NTOS kernel (CVE-2021-33771, CVE-2021-31979)
- 2 Win32k (CVE-2021-1732, CVE-2021-40449)
- 1 Windows update medic (CVE-2021-36948)
- 1 SuperFetch (CVE-2021-31955)
- 1 dwmcore.dll (CVE-2021-28310)
- 1 ntfs.sys (CVE-2021-31956)
iOS/macOS: From 2021, Apple started annotating their release notes with in-the-wild status of vulnerabilities. 5 iOS in-the-wild 0-days were detected and disclosed this year. The first publicly known macOS in-the-wild 0-day (CVE-2021-30869) was also found.
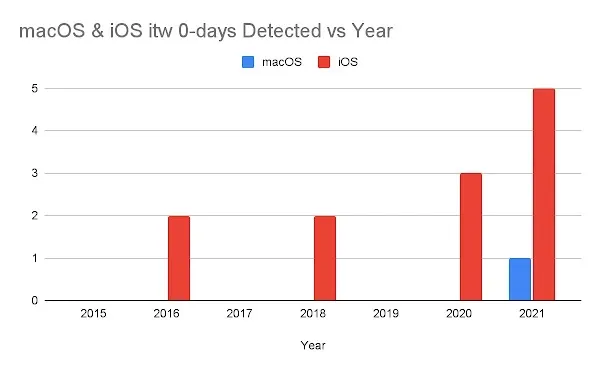
For the 5 total iOS and macOS in-the-wild 0-days, they targeted 3 different attack surfaces:
- IOMobileFrameBuffer (CVE-2021-30807, CVE-2021-30883)
- XNU Kernel (CVE-2021-1782 & CVE-2021-30869)
- CoreGraphics (CVE-2021-30860)
- CommCenter (FORCEDENTRY sandbox escape - CVE requested, not yet assigned)
Android: There were 7 Android in-the-wild 0-days detected and disclosed this year. Prior to 2021, there had only been 1 and it was in 2019: CVE-2019-2215. Like WebKit, this lack of data makes it hard for us to assess trends and changes. Instead, we’ll compare it to public security research.
For the 7 Android 0-days they targeted the following components:
- Qualcomm Adreno GPU driver (CVE-2020-11261, CVE-2021-1905, CVE-2021-1906)
- ARM Mali GPU driver (CVE-2021-28663, CVE-2021-28664)
- Upstream Linux kernel (CVE-2021-1048, CVE-2021-0920)
Microsoft Exchange Server: In 2021, there were 5 in-the-wild 0-days targeting Microsoft Exchange Server. This is the first time any Exchange Server in-the-wild 0-days has been detected and disclosed since we began tracking in-the-wild 0-days.
The first four (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065) were all disclosed and patched at the same time and used together in a single campaign HAFNIUM. The fifth (CVE-2021-42321) was first demonstrated at Tianfu Cup and then discovered in-the-wild by Microsoft.
Later, Microsoft had patched it in November 2021 update.
The attackers required at least another 0-day for successful exploitation since CVE-2021-42321 is a post-authentication bug. Of the four Exchange in-the-wild 0-days used in the first campaign, CVE-2021-26855, which is also known as “ProxyLogon”, is the only one that’s pre-auth.
Despite the number of 0-days found in 2021, there are some popular messaging applications like WhatsApp, Signal, Telegram, etc. are targets of interest to attackers. In these, there is a zero-click zero-day bug in iMessage, which was found in 2021.