Lapsus hacker group which has recently hacked NVIDIA and leaked its user information, other internal tools, and software source code now claimed to hack Samsung Network.
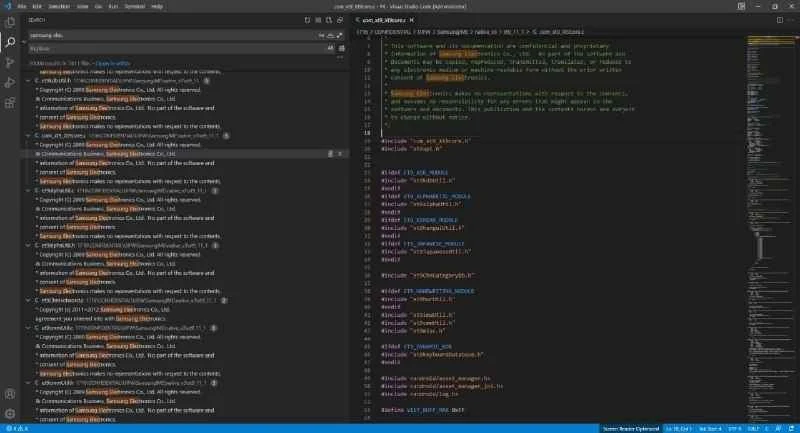
Just an hour ago, the LAPSUS group posted an update on hacking Samsung and leaked Samsung's confidential source code including other confidential data too. Hacker release the hacked data in a torrent file, which have a readme.txt file. Approx 195 GB of data has been leaked by hackers.
Part 1 contains a source code dump and related data about Security/Defense/Knox/Bootloader/ TrustedApps and other items.
Part 2 contains a dump of source code and related data about device security and encryption-related stuff.
Part 3 contains various repositories from Samsung Github. Including Mobile defence engineering, Samsung account backend, Samsung pass backend/frontend, and SES (Bixby, Smartthings, store, etc)
Parts, 1 and 2 also contain highly confidential data from mobile chipmaker giants Qualcomm and various other Samsung partners. What data has been leaked from Qualcomm and which partners, the hackers are talking about is yet to see.
Additionally, hackers categorize the leaks as containing-
Devices & Hardware category
- Source code for every Trusted Applet (TA) installed on all Samsung devices TrustZone (TEE) with specific code for every type of TEE OS (QSEE, TEEGris, etc). This also includes DRM Modules and KEYMASTER/GATEKEEPER source codes.
- Algorithms for all biometric unlock operations, including source code that communicates directly with the sensor
- Bootloader source code for all recent Samsung devices, including Knox data and code for authentication
- Various other data, confidential source code from Qualcomm
Online Services category
- Samsung activation servers source code which was mainly used for the first-time setup of the device.
- Complete Source code of Samsung Accounts which includes Authentication, Identity, API, Services, and many more.
- Various miscellaneous confidential data
The data leak will affect the trust rating of different companies and consumers. Companies do not want to experience the same thing which is why hiring the right RoR developers will make a lot of difference. No company would like private and sensitive data to be released without their consent.
You can expect the following from RoR developers:
- The written code will be more complex and will also be safer.
- Expect high-performing web platforms to be created well.
- Great understanding of the Ruby language and framework.
- Ruby on Rails is a more complex type of framework that is chosen by a lot of popular companies because it can improve the company’s overall security.
The right developers will make sure that all of the tasks that they need to do can be done properly. Tasks can always be checked and rechecked to improve overall data and security. Developers and programmers may need direction in doing different tasks that are set out to do.
The CTO or Chief Technology Officer will serve as the leader of the team. Companies can consider getting CTO permanent hires to ensure that the team will become happier, more productive, and more motivated. A great team with team members that are working well together will continuously improve the security of the website or the app to prevent data leaks.