This vulnerability in HTTP/2 is now identified as CVE-2023-44487, and the successful exploitation of the attack was made possible by abusing some features of the HTTP/2 protocol and server implementation details.
The HTTP/2 protocol allows a denial of service (server resource consumption) because request cancellation can reset many streams quickly, as exploited in the wild in August through October 2023.
What is the HTTP/2 Rapid Reset Vulnerability?
The novel zero-day vulnerability attack, dubbed "HTTP/2 Rapid Reset", exploits the stream cancellation feature built into the HTTP/2 protocol. HTTP/2 allows clients to open multiple streams over a single connection and send requests in parallel over each stream.
Normally, clients have to wait for a response before opening additional streams. However, HTTP/2 also allows clients to unilaterally cancel a stream by sending an RST_STREAM frame.
This zero-day provided threat actors with a critical new tool in their Swiss Army knife of vulnerabilities to exploit and attack their victims at a magnitude that has never been seen before. While at times complex and challenging to combat, these attacks allowed Cloudflare the opportunity to develop purpose-built technology to mitigate the effects of the zero-day vulnerability. - Cloudflare wrote on the blog post.
Attackers have found that rapidly opening streams and immediately canceling them via RST_STREAM frames can overwhelm servers. Even though the streams are canceled, servers still have to do significant processing like parsing headers and mapping URLs for each one.
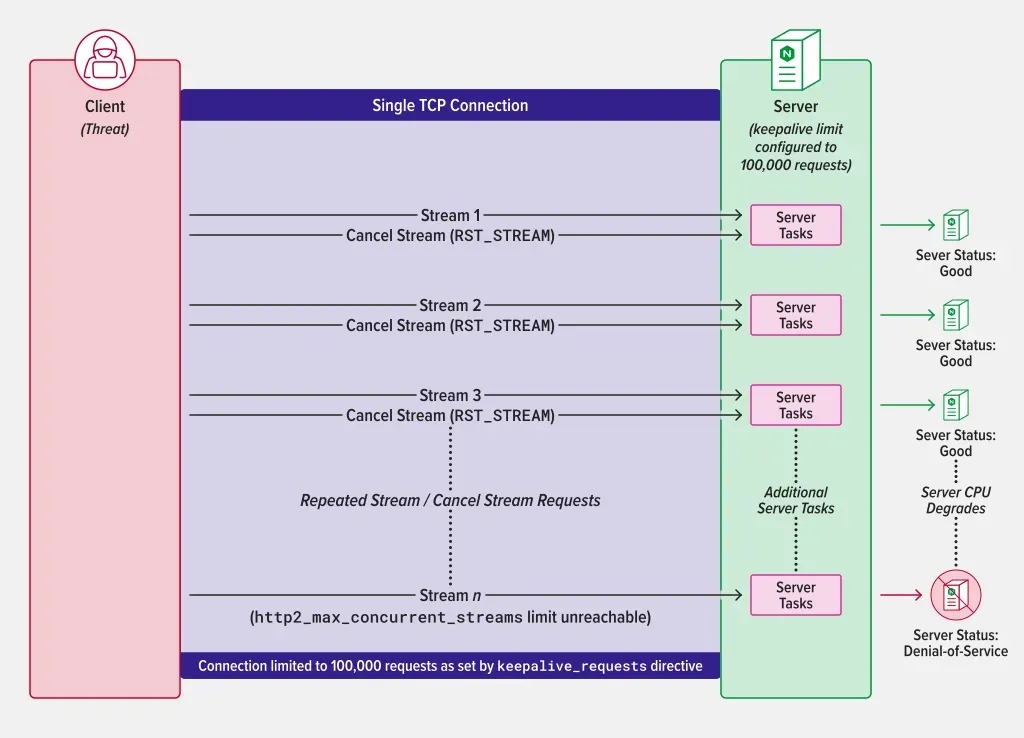 |
| Denial-of-service by establishing HTTP/2 streams, followed by stream cancellations under abnormally high keepalive limits. Credit- Nginx |
How Does it Enable DDoS Attacks?
An unknown threat actor developed an exploit for zero-day vulnerability in the standard HTTP/2 protocol — a fundamental protocol that is critical to how the Internet and all websites work.
This zero-day vulnerability attack leverages HTTP/2’s stream cancellation feature by sending a request and immediately canceling it over and over.
By automating this trivial “request, cancel, request, cancel” pattern at scale, threat actors are able to create a denial of service and take down any server or application running the standard implementation of HTTP/2. Furthermore, one crucial thing to note about the record-breaking attack is that it involved a modestly-sized botnet, consisting of roughly 20,000 machines.
By removing round-trip time as a bottleneck, the rapid reset technique allows almost unlimited requests to be sent over a single HTTP/2 connection.
Normal HTTP/2 connections allow around 100 requests per round-trip time. However, the rapid reset approach enables hundreds of millions of requests per second over a single connection.
Attackers only need relatively small botnets to conduct enormous attacks. Cloudflare reported mitigating 201 million requests per second DDoS attack conducted using a botnet of only around 20,000 machines.
How to Check If Server is Vulnerable to CVE-2023-44487
Currently, a security researcher, Daniel Bloom has released a tool in GitHub written in Python to check if web servers may be vulnerable to CVE-2023-44487
Record-Breaking Attacks Reported
Cloudflare disclosed mitigating DDoS attacks over 200 million requests per second and over 1,100 separate attacks peaking above 10 million requests per second since August 2022.
Google also reported facing similar record-breaking attacks up to 400 million requests per second against its infrastructure, though services were not significantly impacted.
Is HTTP/3 Affected by Rapid Reset Attack?
It is not clear that HTTP/3 (QUIC) is also affected by this attack, but Google did mention the small statements regarding HTTP/3 with recommendations.
We do not believe these attack methods translate directly to HTTP/3 (QUIC) due to protocol differences, and Google does not currently see HTTP/3 used as a DDoS attack vector at scale. Despite that, our recommendation is for HTTP/3 server implementations to proactively implement mechanisms to limit the amount of work done by a single transport connection, similar to the HTTP/2 mitigations discussed above. - Google statement
Mitigations Under Development
Both Cloudflare and Google note that mitigations involve tracking connection statistics to identify abusive connections and immediately terminate them.
The companies coordinated disclosure to allow other major infrastructure providers time to implement protections before public release. But now that details are public, all organizations with HTTP/2 services need to urgently audit their exposure and implement appropriate safeguards.
Cyber Kendra is trying to keep the list of the affected products. At the time of writing this post, Nginx (part of F5) has confirmed that this vulnerability impacts the NGINX HTTP/2 module (ngx_http_v2_module). F5 has also released the security advisory for its multiple products which you can check on this advisory page.
Vendor response for HTTP/2 Rapid Reset Vulnerability
- Cloudflare
- Ngnix
- F5 - (BIG-IP, BIG-IP Next CNF, and BIG-IP Next SPK)
- Amazon AWS
- Envoy Proxy
- HaProxy
- Jetty Proxy
- Swift-nio-http2
- nghttp2
- Netty
- Alibaba - Tengine
- Hyper - An HTTP library for Rust
- Apache - Tomcat
- Caddy Server
- Icing mod_h2
- Microsoft
- Proxmox [not affected]
- Facebook - Proxygen
- HTTP2-rst-Stream
- H2O