
Security vendor 'WithSecure' F-Secure’s enterprise security arm published the report on an ongoing operation (dubbed "DUCKTAIL") that targets individuals and organizations that operate on Facebook’s Business and Ads platform.
According to the WithSecure report, the operation is conducted by a Vietnamese threat actor and the threat actor targets individuals and employees that may have access to a Facebook Business account with information-stealer malware.
"The malware is designed to steal browser cookies and take advantage of authenticated Facebook sessions to steal information from the victim's Facebook account and ultimately hijack any Facebook Business account that the victim has sufficient access to."
WithSecure Analysis on DUCKTAIL
Based on telemetry and investigation conducted by WithSecure, one approach employed by the threat actor is to scout for companies that operate on Facebook’s Business/Ads platform and directly target individuals within the company/business that might have high-level access to the Facebook Business.
WithSecure Countercept Detection and Response team has identified instances where the malware was delivered to victims through LinkedIn. These tactics would increase the adversary’s chances of compromising the respective FacebookBusiness all the while flying under the radar. Some of the observed samples have been hosted on file or cloud hosting services, such as Dropbox, iCloud, and MediaFire.
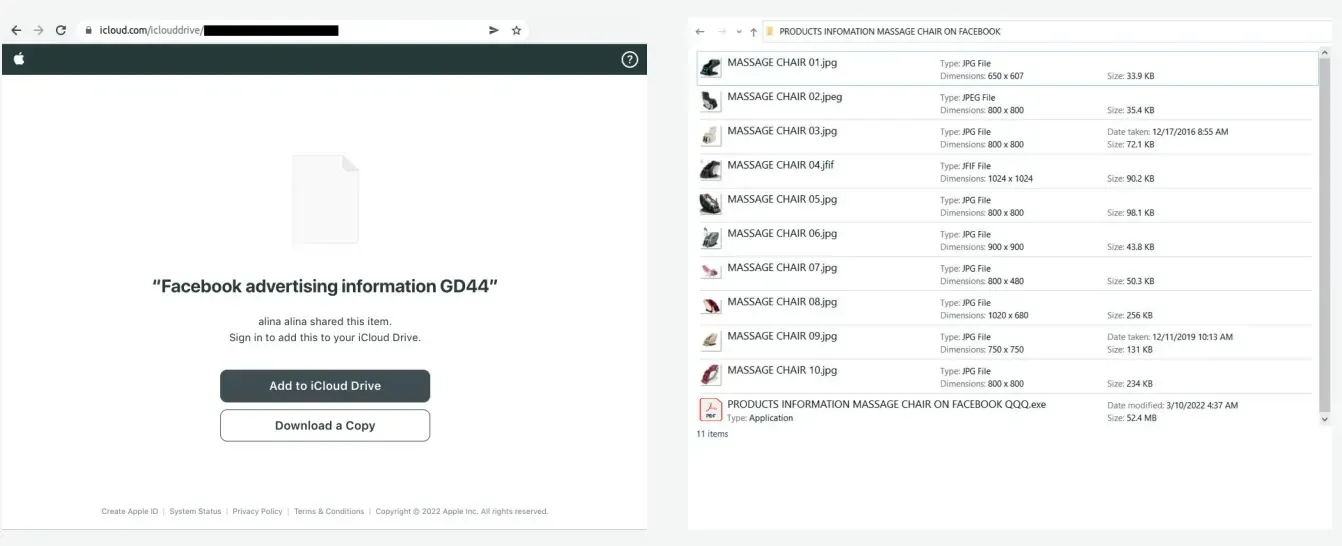 |
| DUCKTAIL malware hosted on iCloud & contents of an archive file sent by the threat actor |
The malware was often delivered as an archive file which contained the malware executable alongside related images, documents, and video files. The content and file names (listed in the appendices section) revealed how the threat actor intended to lure victims into launching their malware.
The file names generally utilized keywords related to brands, products, and project planning. Some examples include: “project development plan, project information, products.pdf.exe” and “new project l'oréal budget business plan.exe”. Moreover, some of the observed samples had country names appended to the file name which indicates that the threat actor tailors the file name based on the target’s locality. This indicates that the threat actor was aware of the victim’s location ahead of time.
Activity of DUCKTAIL
The malware appears to have been coded using .NET Core and d were compiled using its single file feature which gets to work scanning victims’ browsers for the presence of Facebook session cookies.
If those cookies are found, the malware “directly interacts with various Facebook endpoints from the victim’s machine using the Facebook session cookie (and other security credentials that it obtains through the initial session cookie) to extract information from the victim’s Facebook account.”
WithSecure’s analysts believe the attacker has been probing Facebook’s security for up to three years and has successfully adapted DUCKTAIL to cope with changes the social network hoped would harden its system.
"We believe this, in addition to the fact that the malware directly interacts with Facebook endpoints from the victim’s machine, is done to circumvent security features implemented by Meta, as activities and actions that are performed from the user's own machine and primary browser likely appear 'benign'."
WithSecure had shared the DUCKTAIL research with Facebook (Meta), on which Facebook provided the following statements -
"We welcome security research into the threats targeting our industry. This is a highly adversarial space and we know these malicious groups will keep trying to evade our detection. We are aware of these particular scammers, regularly enforce against them, and continue to update our systems to detect these attempts. Because this malware is typically downloaded off-platform, we encourage people to be cautious about what software they install on their devices."
A full report containing a detailed analysis of DUCKTAIL’s malware, recommendations, and protection, including indicators of compromise, detection opportunities, and MITRE ATT&CK techniques can be found in the [PDF] report.