
The vulnerability dubbed CVE-2022-21445 (CVSS score of 9.8) is an untrusted data deserialization vulnerability that can be used to execute arbitrary code on the victim's system.
Researchers Peterjson at VNG Corporation and Nguyen Jang at VNPT discovered CVE-2022-21445 in the ADF Faces framework in October 2021 and reported it to Oracle. However, the company did not release a fix until six months later, as part of the April Critical Patch Update.
According to the researchers, the RCE vulnerability, which they called a "Miracle" vulnerability, affects all applications using the ADF Faces framework, including Business Intelligence, Enterprise Manager, Identity Management, SOA Suite, WebCenter Portal, Application Testing Suite and Transportation Management.
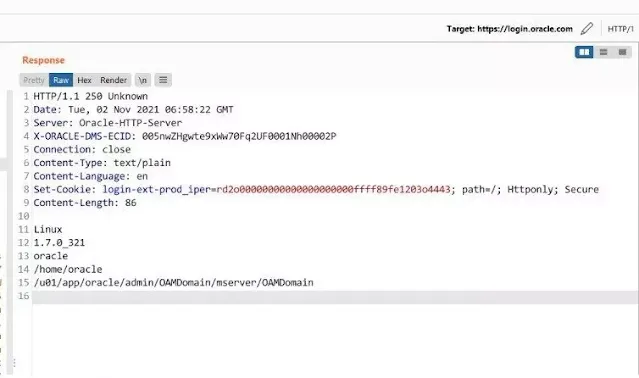
The researchers also found CVE-2022-21497 (with a CVSS score of 8.1), and SSRF vulnerability that can be used in conjunction with CVE-2022-21445 to remotely execute code before logging in to Oracle Access Manager.
Exploiting these vulnerabilities, the researchers developed an exploit they called the Miracle Exploit. According to them, all online systems and Oracle cloud services using ADF Faces are subject to vulnerabilities.